Proxies
A proxy is an intermediary server that sits between a client and a destination server. Instead of communicating directly, the client talks to the proxy, which forwards the request on the client’s behalf (or on the server’s behalf, depending on the type). Proxies are fundamental building blocks in system design, appearing in caching layers, load balancers, security infrastructure, and service meshes.
There are two main types of proxies: forward and reverse. In the industry, people tend to use the term “proxy” loosely, usually meaning a forward proxy without saying “forward” explicitly. Understanding the distinction between the two is essential.
Forward Proxy
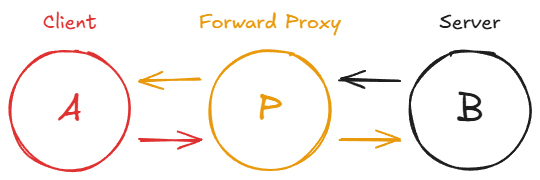
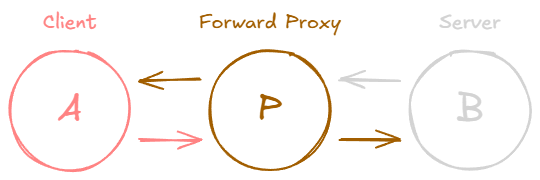
A forward proxy acts on behalf of the client. The client sends its request to the proxy, and the proxy forwards it to the destination server. The server sees the request as coming from the proxy’s IP address, not the client’s.
From the server’s perspective, the client is invisible. The server knows only that the proxy made the request. This is the basic principle behind how VPNs work: traffic is routed through an intermediary so the destination server cannot see the client’s real IP address.
Forward proxies serve several practical purposes:
- Corporate firewalls and access control: Organizations route all employee internet traffic through a forward proxy to enforce security policies, block malicious websites, and log activity for compliance.
- Content filtering: Schools and libraries use forward proxies to restrict access to certain categories of websites.
- Bypassing geographic restrictions: Users can route their traffic through a forward proxy in a different region to access content that is otherwise geo-blocked.
Reverse Proxy
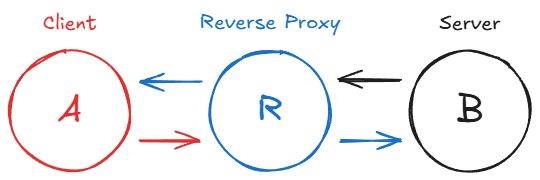
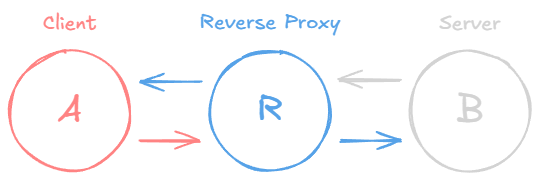
A reverse proxy acts on behalf of the server. The client sends its request to what it believes is the server, but the request actually arrives at the reverse proxy. The proxy then forwards it to one of potentially many backend servers and returns the response to the client.
The key difference from a forward proxy: with a forward proxy, the server does not know who the real client is. With a reverse proxy, the client does not know which backend server is actually handling the request. The client thinks it is talking directly to the server.
For example, when you type google.com in your browser, the DNS lookup returns the IP address of a reverse proxy (or load balancer), not an individual backend server. Your browser has no idea how many servers sit behind that single address.
Because the reverse proxy is the one making requests to the backend, the backend server only sees the proxy’s IP address. To preserve the original client’s IP, reverse proxies typically add the X-Forwarded-For header to forwarded requests. This lets the backend know who actually initiated the connection.
A minimal Nginx reverse proxy configuration looks like this:
1
2
3
4
5
6
location / {
proxy_pass http://backend_server;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
}
Reverse Proxy Use Cases
Reverse proxies are one of the most versatile tools in system design:
- Load balancing: Distributing incoming requests across multiple backend servers to prevent any single server from being overwhelmed. This also provides resilience: if one server goes down, the proxy routes traffic to the remaining healthy servers.
- TLS termination: Handling the encryption/decryption of HTTPS traffic so that backend servers deal only with unencrypted HTTP internally, reducing their CPU load.
- Caching: Storing responses for frequently requested resources (HTML pages, API responses, static assets) and serving them directly without hitting the backend.
- Request filtering and rate limiting: Blocking malicious requests, enforcing rate limits, or rejecting requests that do not meet certain criteria before they reach the application servers.
- Compression: Compressing responses before sending them to clients to reduce bandwidth usage.
Transparent Proxy
A transparent proxy intercepts network traffic without the client being aware of its existence. Unlike a traditional forward proxy, the client does not need to be configured to use it. The proxy sits inline on the network path and intercepts requests automatically. Transparent proxies are commonly deployed by ISPs for caching popular content, by organizations for monitoring network usage, and in CDN architectures to route requests to the nearest edge server.
Common Proxy Software
- Nginx: A high-performance web server frequently used as a reverse proxy and load balancer. It excels at serving static content and terminating TLS connections.
- HAProxy: A dedicated, high-performance TCP/HTTP load balancer and reverse proxy known for its reliability in high-traffic production environments.
- Envoy: A modern, cloud-native proxy originally built at Lyft. It is widely used as a sidecar proxy in service mesh architectures (e.g., Istio) and provides advanced observability, traffic management, and security features.
- Squid: A caching and forwarding HTTP proxy commonly used for web content caching and access control.
Related posts: Load Balancing, Caching, Network Protocols